Tutorial B5 Breaking AES (Straightforward)
This tutorial has been updated for ChipWhisperer 4.0.0 release. If you are using 3.x.x see the "V3" link in the sidebar.
| B5: Breaking AES (Straightforward) | |
|---|---|
| Target Architecture | XMEGA |
| Hardware Crypto | No |
| Software Release | V3 / V4 / V5 |
This tutorial will take you through a complete attack on a software AES implementation. The specific implementation being attacked is a well-known AES implementation written in C, which is likely to be similar to other implementations used by proprietary systems.
Capturing
This tutorial runs on four different hardware targets. You only need to follow the steps for your given hardware.
Capturing with ChipWhisperer-Lite/Pro with default XMEGA Target (CW303)
NOTE: You can see a Quick-Start Guide and Video for this target on the CW1173_ChipWhisperer-Lite page:
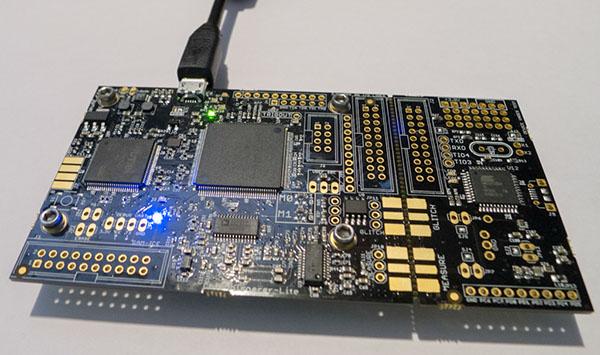
Hardware Setup
Connect the CW1173/CW1200 by USB cable to computer.
- The software AES implementation that will run on the target is located in
chipwhisperer\hardware\victims\firmware\simpleserial-aes. In a terminal window, navigate here and run the commandmaketo build the firmware. As in previous tutorials, ensure that the firmware has been built for the correct board. Here, the output ofmakeshould end likeAVR Memory Usage ---------------- Device: atxmega128d3 Program: 3078 bytes (2.2% Full) (.text + .data + .bootloader) Data: 352 bytes (4.3% Full) (.data + .bss + .noinit) Built for platform CW-Lite XMEGA -------- end --------
Make sure that the platform is correct.
- Upload the firmware to the target chip. The process to do this is the same as the previous tutorials:
- Open the ChipWhisperer Capture software.
- Connect to the ChipWhisperer. (You can do this using a script or by filling out the generic settings and connecting to the board yourself.)
- Open the XMEGA Programmer (**Tools > ChipWhisperer-Lite XMEGA Programmer**).
- Find the hex file you compiled and program it onto the target.
Capturing the Traces
- Close & reopen the capture software (to clear out any previous connection which may be invalid).
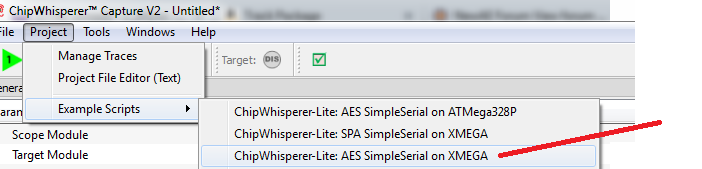
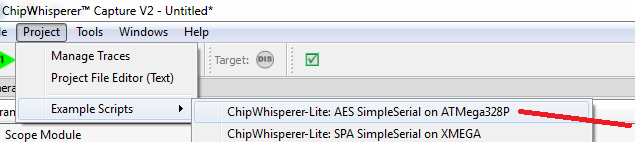
From the Project menu elect the Example Scripts and then ChipWhisperer-Lite: AES SimpleSerial on XMEGA (make sure you don't select the "SPA" example):
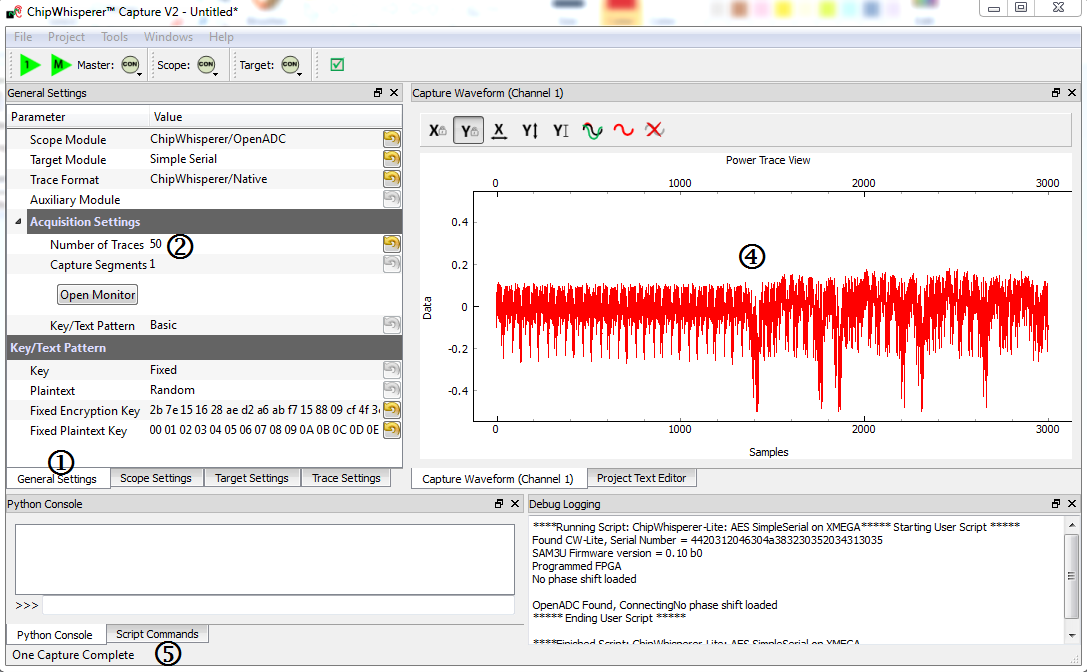
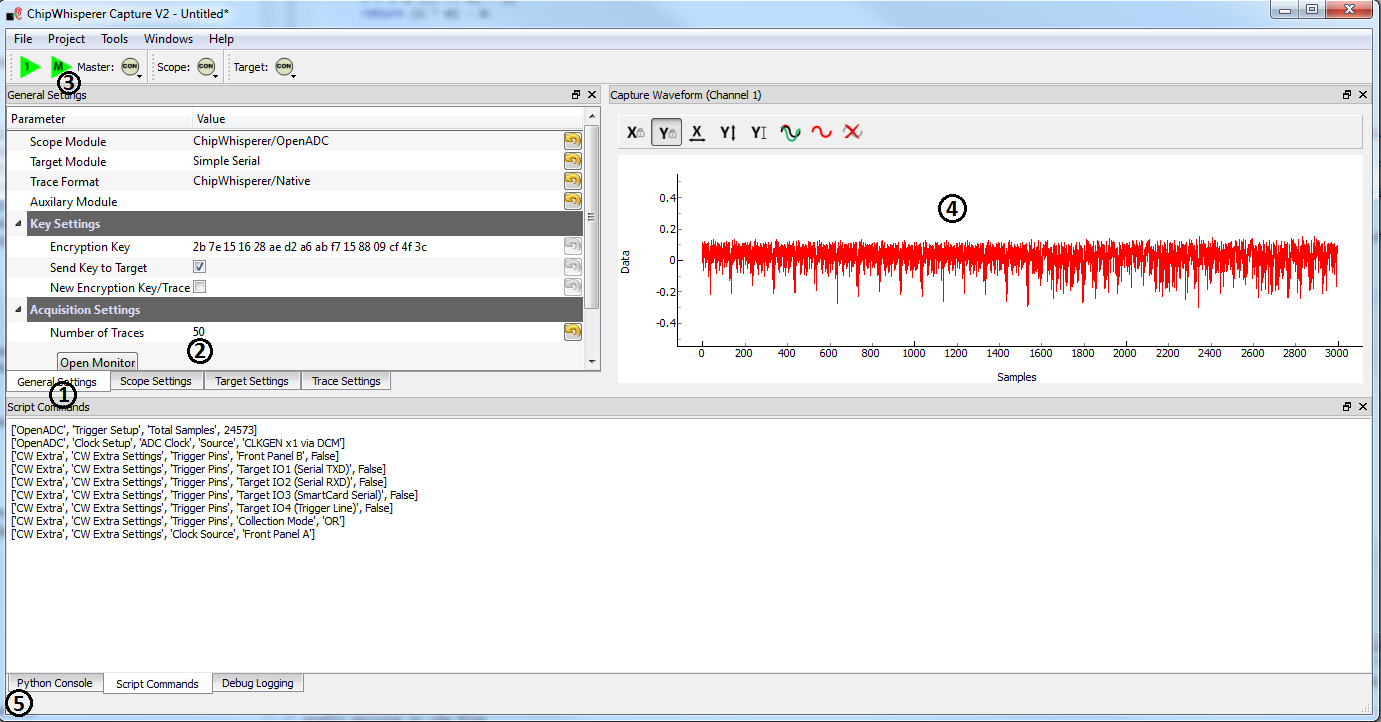
The script will automatically connect to the capture hardware and run 2 example traces. You should see something that looks like the following screen:
To complete the tutorial, follow these steps:
- Switch to the General Settings tab
- If you wish to change the number of traces, do so here. The default of 50 should be sufficient to break AES though!
- Hit the Capture Many button (M in a green triangle) to start the capture process.
- You will see each new trace plotted in the waveform display.
- You'll see the trace count in the status bar. Once it says Trace 50 done (assuming you requested 50 traces) the capture process is complete.
- Finally save this project using the File --> Save Project option, give it any name you want.
- Skip ahead to #Analyzing_the_Traces.
Capturing with ChipWhisperer-Lite/Pro with NOTDuino (CW304)
Hardware Setup
Capturing the Traces
- Close & reopen the capture software (to clear out any previous connection which may be invalid).
From the Project menu elect the Example Scripts and then ChipWhisperer-Lite: AES SimpleSerial on ATMega328P
The script will automatically connect to the capture hardware and run 2 example traces. You should see something that looks like the following screen:
To complete the tutorial, follow these steps:
- Switch to the General Settings tab
- If you wish to change the number of traces, do so here. The default of 50 should be sufficient to break AES though!
- Hit the Capture Many button (M in a green triangle) to start the capture process.
- You will see each new trace plotted in the waveform display.
- You'll see the trace count in the status bar. Once it says Trace 50 done (assuming you requested 50 traces) the capture process is complete.
- Finally save this project using the File --> Save Project option, give it any name you want.
- Skip ahead to #Analyzing_the_Traces.
Capturing with Capture Rev2 + Multi-Target (CW1002 + CW301)
Hardware Setup
This tutorial uses the CW1002_ChipWhisperer_Capture_Rev2 hardware along with the CW301_Multi-Target board. Note that you don't need hardware to complete the tutorial. Instead you can download example traces from the ChipWhisperer Site.
This example uses the Atmel AVR in 28-pin DIP programmed with a simpleserial communications protocol. This is the default firmware programmed into the devices, so you shouldn't need to do anything. If you've erased the device, you can see programming instructions in the Installing_ChipWhisperer section.
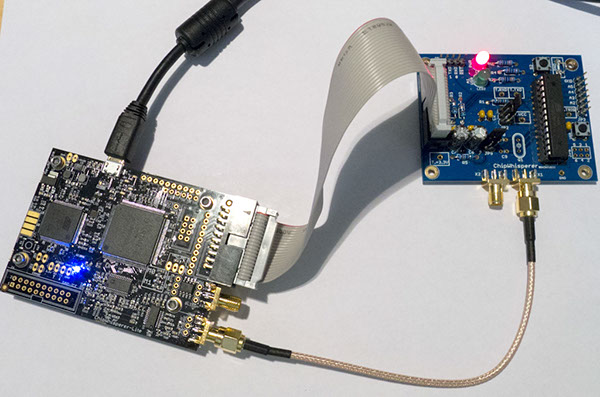
The Multi-Target board should be plugged into the ChipWhisperer Capture Rev2 via the 20-pin target cable. The VOUT SMA connector is wired to the LNA input on the ChipWhisperer-Capture Rev2 front panel. The general hardware setup is as follows:
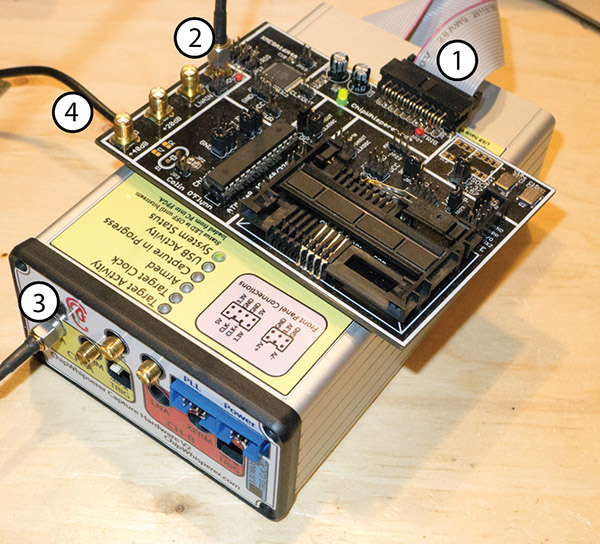
- 20-Pin Header connects Multi-Target to Capture Hardware
- VOUT Connects to SMA Cable
- SMA Cable connects to 'LNA' on CHA input
- USB-Mini connects to side (NB: Confirm jumper settings in next section first)
Jumpers on the Multi-Target Victim board are as follows:
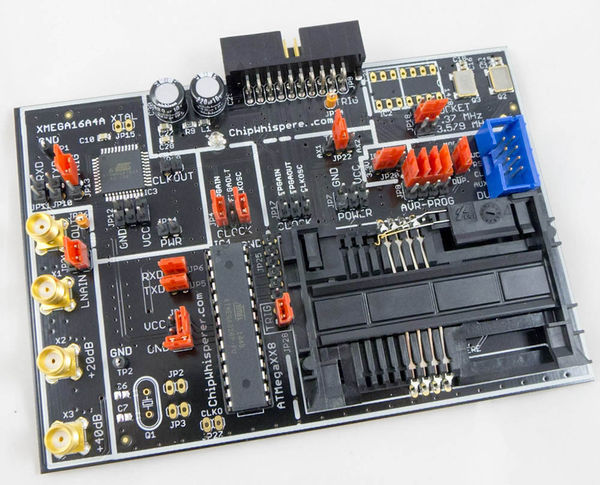
- NO jumpers mounted in XMEGA Portion or SmartCard Portion (JP10-JP15, JP19, JP7-JP8, JP17)
- 3.3V IO Level (JP20 set to INT.)
- The 7.37 MHz oscillator is selected as the CLKOSC source (JP18)
- The CLKOSC is connected to the AVR CLock Network, along with connected to the FPGAIN pin (JP4)
- The TXD & RXD jumpers are set (JP5, JP6)
- Power measurement taken from VCC shunt (JP1)
- The TRIG jumper is set (JP28) (NOTE: Early revisions of the multi-target board do not have the TRIG jumper and you can ingore this).
For more information on these jumper settings see CW301_Multi-Target .
Setting up the Software
It is assumed that you've already followed the guide in Installing_ChipWhisperer. Thus it is assumed you are able to communicate with the ChipWhisperer Capture Rev2 hardware. Note in particular you must have configured the FPGA bitstream in the ChipWhisperer-Capture software, all part of the description in the Installing_ChipWhisperer guide.
Capturing the Traces
This tutorial uses a simple script that ships with the ChipWhisperer Capture software. The easiest method of accomplishing the trace capture is as follows:
- Close & reopen the capture software (to clear out any previous connection which may be invalid).
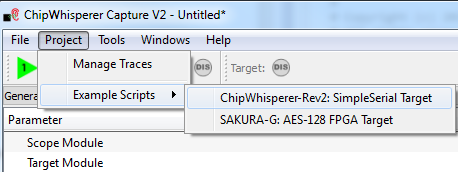
From the Project menu elect the Example Scripts and then ChipWhisperer-Rev2: SimpleSerial Target
The script will automatically connect to the capture hardware and run 2 example traces. You should see something that looks like the following screen:
To complete the tutorial, follow these steps:
- Switch to the General Settings tab
- If you wish to change the number of traces, do so here. The default of 50 should be sufficient to break AES though!
- Hit the Capture Many button (M in a green triangle) to start the capture process.
- You will see each new trace plotted in the waveform display.
- You'll see the trace count in the status bar. Once it says Trace 50 done (assuming you requested 50 traces) the capture process is complete.
- Finally save this project using the File --> Save Project option, give it any name you want.
- Skip ahead to #Analyzing_the_Traces.
Capturing with PicoScope + Multi-Target (CW301)
<TODO>
Analyzing the Traces
- Open the Analyzer software
- From the File --> Open Project option, navigate to the .cwp file you save previously. Open this file.
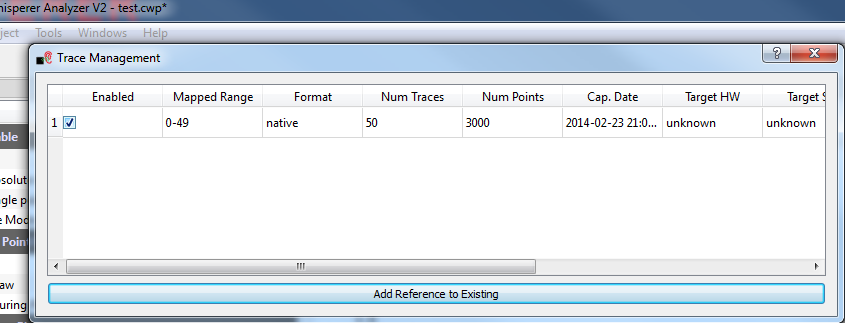
Select the Project --> Manage Traces option to open the dialog, enable the captured traces by adding a check-mark in the box. Close the dialog with `ESC`:
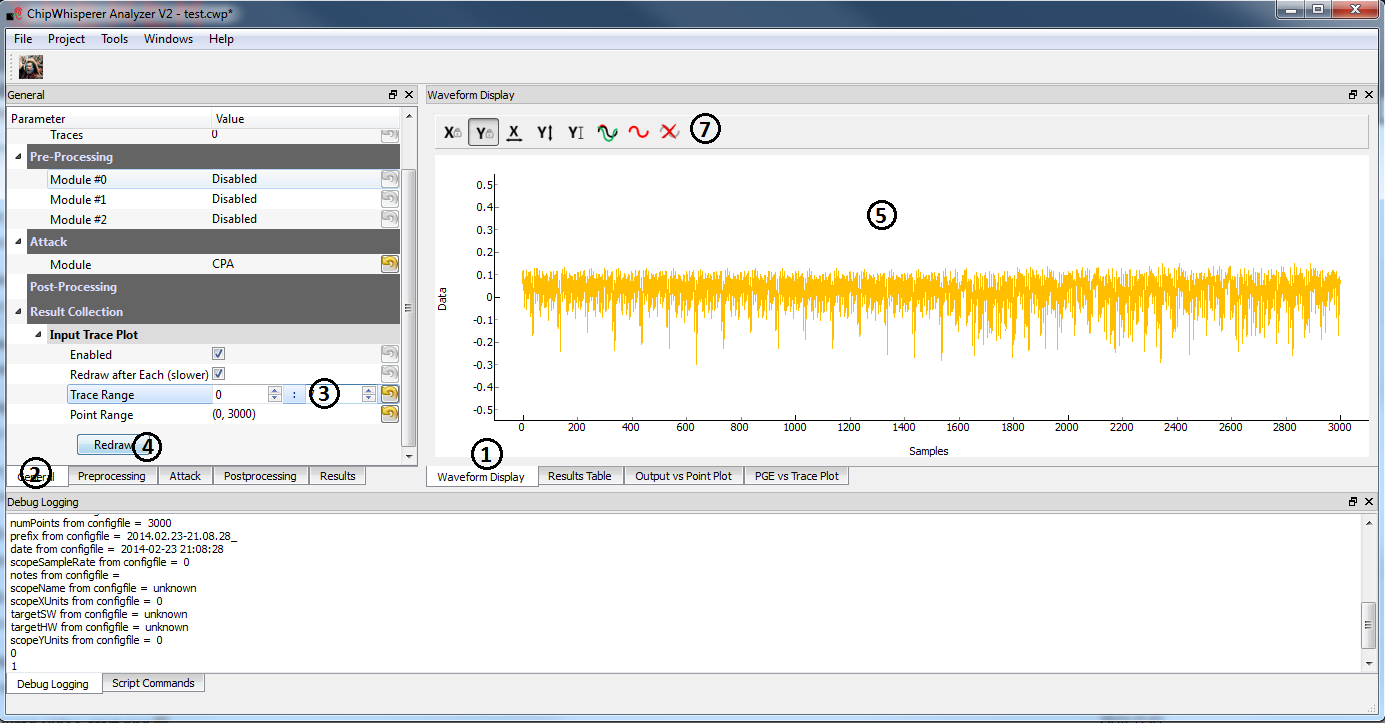
If you wish to view the trace data, follow these steps:
- Switch to the Waveform Display tab
- Switch to the General parameter setting tab
- You can choose to plot a specific range of traces
- Hit the Redraw button when you change the trace plot range
- You can right-click on the waveform to change options, or left-click and drag to zoom
- (oops there is no 6)
- Use the toolbar to quickly reset the zoom back to original
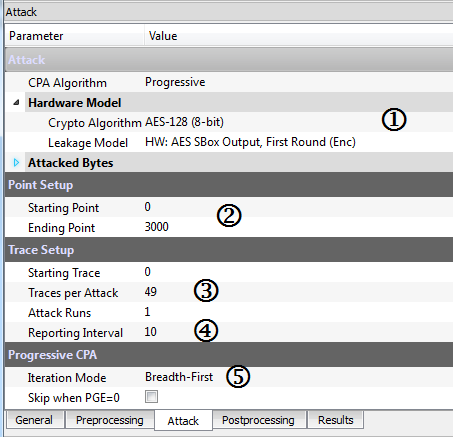
You can view or change the attack options on the Attack parameter settings tab:
- The Hardware Model settings are correct for the software AES by default
- The Point Setup makes the attack faster by looking over a more narrow range of points. Often you might have to characterize your device to determine the location of specific attack points of interest.
- Traces per Attack allows you to use only a subset of capture traces on each attack. Or if you have for example 1000 traces, you could average the results of attacking 50 traces over 200 attack runs.
- Reporting Interval is how often data is generated. A smaller interval generates more useful output data, but greatly increases computational complexity (e.g. slows down attack). If you only care about attacking the system, the reporting interval can be set to the number of traces. In which case the attack runs completely, and you get the results. For this tutorial you can set to a smaller number (such as 5).
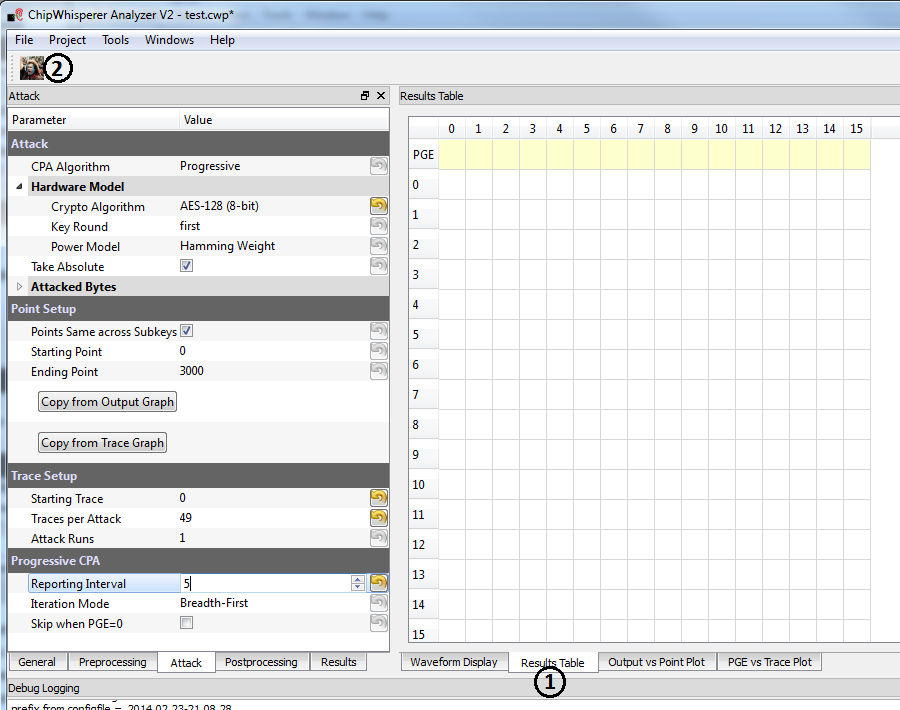
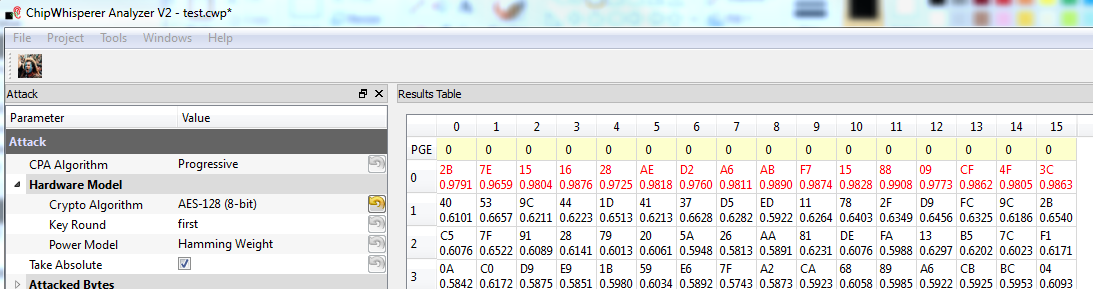
Finally run the attack by switching to the Results Table tab and then hitting the Attack button:
If you adjusted the Reporting Interval to a smaller number such as 5, you'll see the progression of attack results as more traces are used. If not you should simply see the final results, which should have the correct key highlighted in red. In the following case the correct key was recovered:
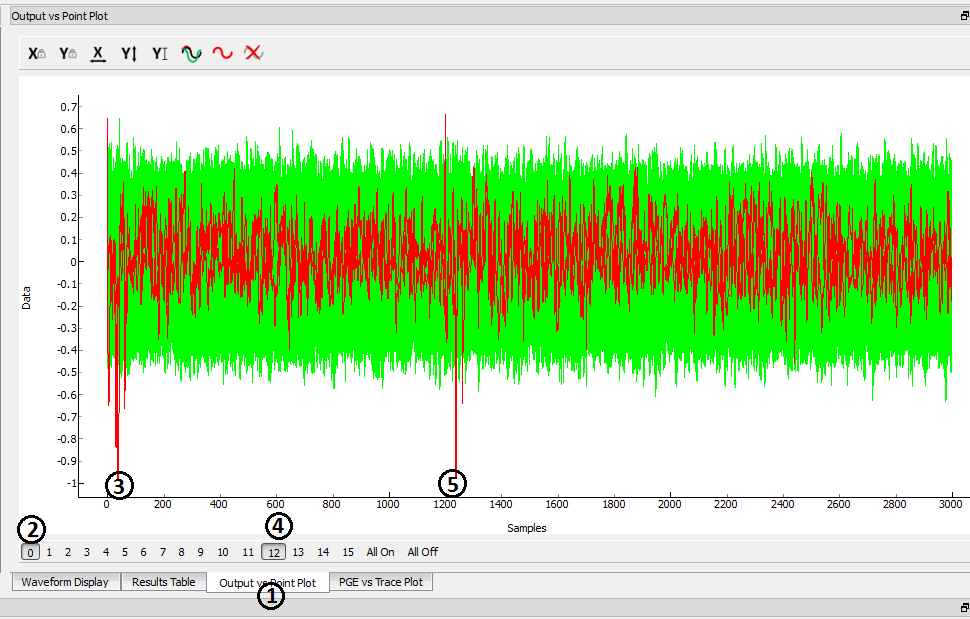
You can also switch to the Output vs Point Plot window to see where exactly the data was recovered:
- Switch to the Output vs Point Plot tab
- Turn on one of the bytes to see results.
- The known correct guess for the key is highlighted in red. The wrong guesses are plotted in green. You can see that the attacked operation appeared to occur around sample 40 for key 0. Remember you can click-drag to zoom in, then right-click and select View All to zoom back out.
- Turn on another byte to see results for it.
- This byte occured much later - sample 1240. By exploring where the maximum correlation was found for the correct key-guess of each byte, you can determine where exactly the attacked operation occured.
Next Steps
This has only briefly outlined how to perform a CPA attack. You can move onto more advanced tutorials, especially showing you how the actual attack works when performed manually.